RedSeal and Rapid7
Add Network Context To Vulnerability Prioritization
Network vulnerability assessments often overwhelm organizations with too many “high” and “critical” results. Compounding this problem is the sheer number of new vulnerabilities that surface each year and the large number of assets that need patching. Add to this the fact that many organizations are still running legacy systems whose vulnerabilities do not have patches. And finally, it is not easy to know whether all network devices were actually scanned.
VULNERABILITY PRIORITIZATION
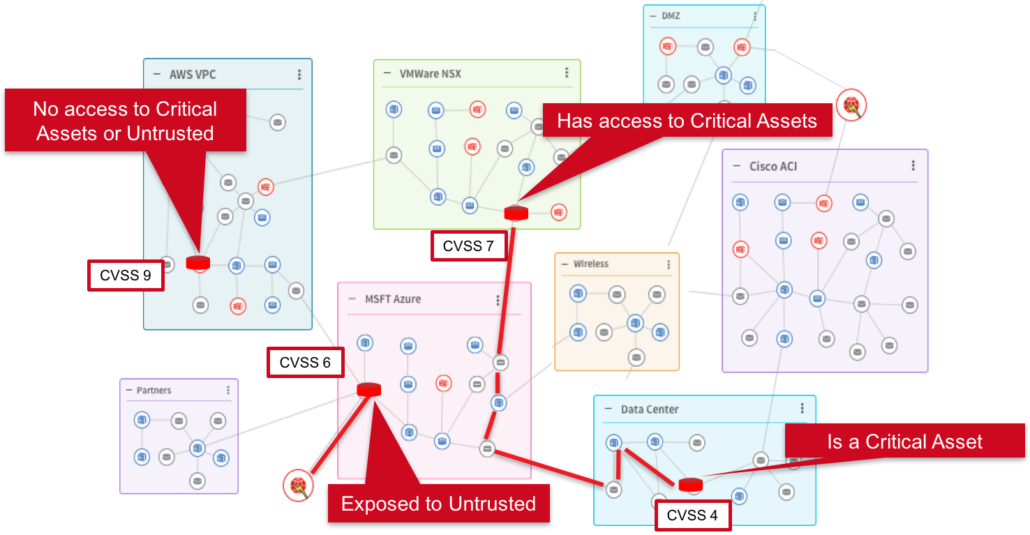
RedSeal and Rapid7 have teamed up to add network context to InsightVM’s vulnerability prioritization. RedSeal looks at three factors to refine:
InsightVM’s initial prioritization:
First, it determines if a vulnerable host can be exploited from an untrusted network. Second, it determines if the vulnerable host can reach and potentially exploit downstream assets. And, third, it factors in the criticality of the assets in question. If access is permitted and assets are of high value, the priority increases. On the other hand, if layered defenses are preventing access and the hosts are not high value, the priority is reduced.
RedSeal prioritizes vulnerable hosts based on access to untrusted networks and the potential to infect other assets:
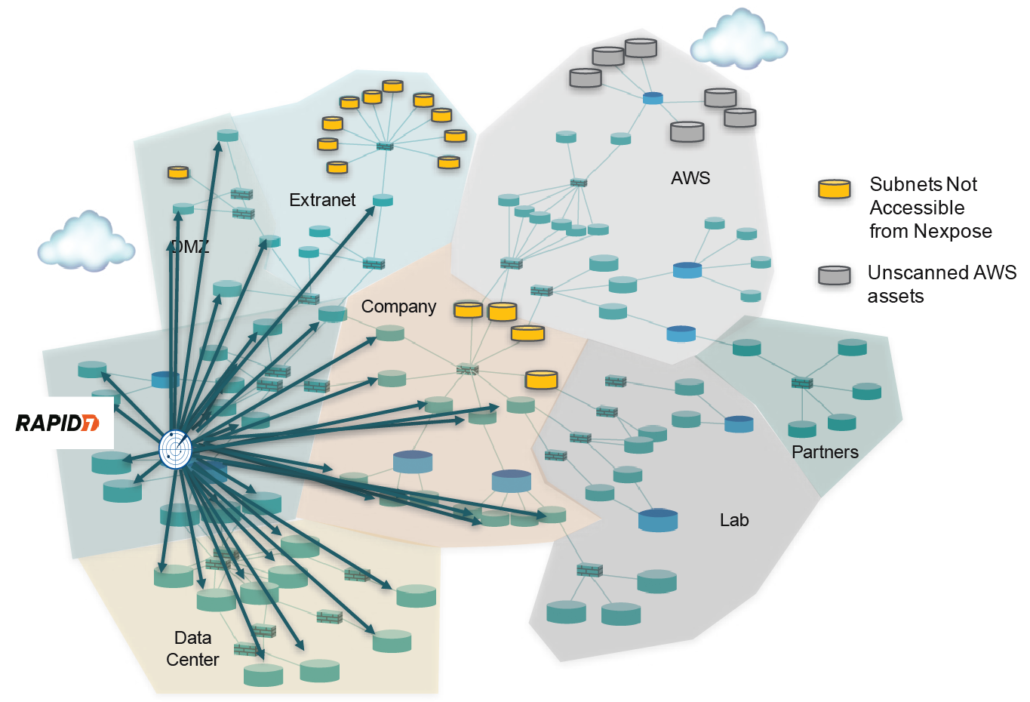
GAPS IN SCAN COVERAGE
RedSeal can determine if all assets have been scanned by InsightVM. It is not uncommon for InsightVM to be denied access by a firewall, access control list (ACL) or other device. RedSeal can query its model and see all the access paths available to InsightVM. If a network segment has not been scanned, RedSeal will show you the unscanned subnet and the firewall rule or ACL that prevented the scan.
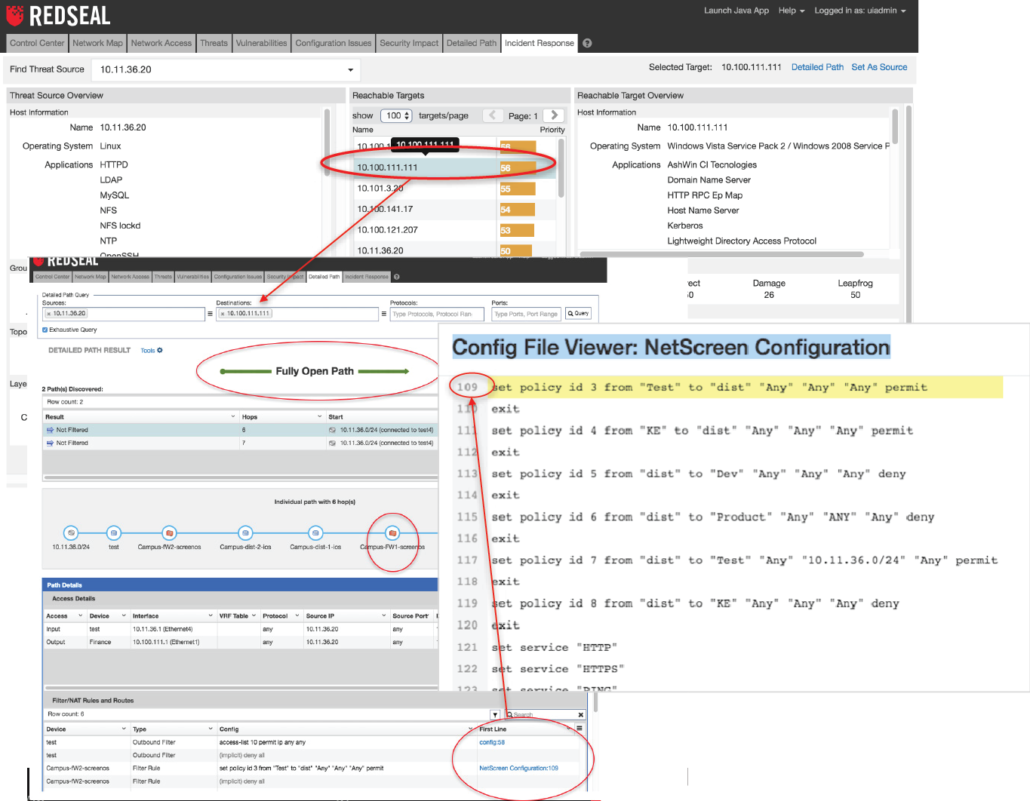
CONTAINMENT
RedSeal can also help when there are no patches available for a legacy system.
RedSeal will identify a firewall, router, switch or other device that can be configured to prevent access to the vulnerable device.
BENEFITS
Mitigate critical threats with targeted patching
Patch vulnerabilities that can be exploited from untrusted networks first
Prioritize hosts that can infect critical downstream assets
Discover gaps in scan coverage
Contain vulnerabilities that don’t have patches
WHAT YOU NEED
RedSeal 8.3
Rapid7 Nexpose 6.4.x
RESOURCES
Solution Brief – RedSeal & Rapid7: Add Network Context To Vulnerability Priorization