Project Zero – A Smarter Way Forward
Google’s move to set up Project Zero is very welcome. The infrastructure on which we run our businesses and our lives is showing its fragile nature as each new, successful attack is disclosed. 
Attacks proliferate rapidly – very rapidly, in a quite robust market for newly found, highly effective vulnerabilities. As they do so, it has become crystal clear that traditional passive, reactive methods of defense are insufficient. Google’s investment underscores the critical importance of proactive analysis of potential attack vectors. Any organization that is not developing a set of defenses from proactive analysis through reactive defenses is leaving the door open to attacks. Defenders need ways to automate – to pick up all the discoveries as they are found by the “good guys”, so they can assess their own risk and keep up with remediation. Recent incidents like Code Spaces and Target make clear that the health of enterprises and the careers of their executives are at stake; just expecting defenses to hold without some way to automate validation is not tenable. Hope is not a strategy.

 I think what worries me more are the organizations who know they have information gaps, but don’t treat them as a priority. I see this as driving a car while blindfolded. How is security possibly going to be effective if you can’t map out the infrastructure – the whole infrastructure, warts, labs, virtualization and all – and just look at it, let alone ask decent, proactive questions about how to defend yourself? Imagine physical security – for example, badge reader installation – without having a map of the building, or even a vague idea of the number of doors that need to be secured.
I think what worries me more are the organizations who know they have information gaps, but don’t treat them as a priority. I see this as driving a car while blindfolded. How is security possibly going to be effective if you can’t map out the infrastructure – the whole infrastructure, warts, labs, virtualization and all – and just look at it, let alone ask decent, proactive questions about how to defend yourself? Imagine physical security – for example, badge reader installation – without having a map of the building, or even a vague idea of the number of doors that need to be secured.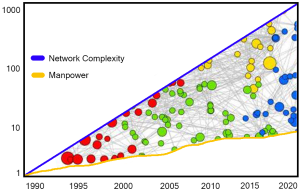 At first, I didn’t want to talk about data gaps – that sounded like a challenge to good analytics. I was half right. Eventually, enough CISO’s got it through my skull that uncovering data gaps may be pointing to reasons why analytics will be held back, but it’s also major value, in and of itself. I was being dense – if we try to analyze security data, and we find it’s got holes in it, well, this means the security team didn’t know what was going on to start with! Turning up these gaps is one of those inconvenient truths. These days we’ve gotten pretty good at it.
At first, I didn’t want to talk about data gaps – that sounded like a challenge to good analytics. I was half right. Eventually, enough CISO’s got it through my skull that uncovering data gaps may be pointing to reasons why analytics will be held back, but it’s also major value, in and of itself. I was being dense – if we try to analyze security data, and we find it’s got holes in it, well, this means the security team didn’t know what was going on to start with! Turning up these gaps is one of those inconvenient truths. These days we’ve gotten pretty good at it.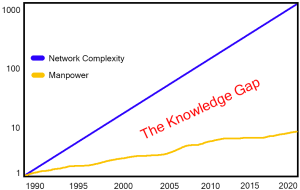 Have you found it easy to hire the talent you need? If so, lucky you – feel free to drop hints in the comments section (or just gloat – your peers tell me they aren’t having it so easy).
Have you found it easy to hire the talent you need? If so, lucky you – feel free to drop hints in the comments section (or just gloat – your peers tell me they aren’t having it so easy).