Advisory Notice: MOVEit Transfer Critical Vulnerability
CVE: CVE-2023-35708
Description:
Progress has discovered a vulnerability in MOVEit Transfer that could lead to escalated privileges and potential unauthorized access to the environment. If you are a MOVEit Transfer customer, it is extremely important that you take immediate action as noted below in order to help protect your MOVEit Transfer environment. In Progress MOVEit Transfer versions released before 2021.0.8 (13.0.8), 2021.1.6 (13.1.6), 2022.0.6 (14.0.6), 2022.1.7 (14.1.7), 2023.0.3 (15.0.3), a SQL injection vulnerability has been identified in the MOVEit Transfer web application that could allow an un-authenticated attacker to gain unauthorized access to the MOVEit Transfer database. An attacker could submit a crafted payload to a MOVEit Transfer application endpoint which could result in modification and disclosure of MOVEit database content.
Recommended Mitigation Steps:
- Disable all HTTP and HTTPs traffic to your MOVEit Transfer environment. More specifically:
-
- Modify firewall rules to deny HTTP and HTTPs traffic to MOVEit Transfer on ports 80 and 443.
- It is important to note that until HTTP and HTTPS traffic is enabled again:
- Users will not be able to log on to the MOVEit Transfer web UI.
- MOVEit Automation tasks that use the native MOVEit Transfer host will not work.
- REST, Java and .NET APIs will not work.
- MOVEit Transfer add-in for Outlook will not work.
- SFTP and FTP/s protocols will continue to work as normal.
-
- As a workaround, administrators will still be able to access MOVEit Transfer by using a remote desktop to access the Windows machine and then accessing https://localhost/. For more information on localhost connections, please refer to MOVEit Transfer Help: https://docs.progress.com/bundle/moveit-transfer-web-admin-help-2023/page/Security-Policies-Remote-Access_2.html
- Apply the Patch
As patches for supported MOVEit Transfer versions become available, links will be provided below. Supported versions are listed at the following link: https://community.progress.com/s/products/moveit/product-lifecycle. Please note, the license file can remain the same when staying on a major release to apply the patch. - Enable all HTTP and HTTPs traffic to your MOVEit Transfer environment
- Please bookmark the Progress Security Page and refer to it to ensure you have all of the latest updates.
How Can RedSeal Help?
- By bringing Host Data into your RedSeal instance, we can identify hosts with the targeted CVE in both the “Endpoint Data” tab, as well as the “Vulnerabilities” tab.
- First be sure to update your CVE definitions on your endpoint scanning system and run a data collection in RedSeal.
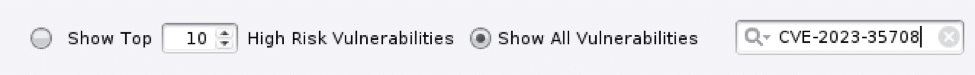
- If the vulnerability does not show up at first, try changing the radio button to “Show All Vulnerabilities”
- Next, search specifically for the CVE in question:
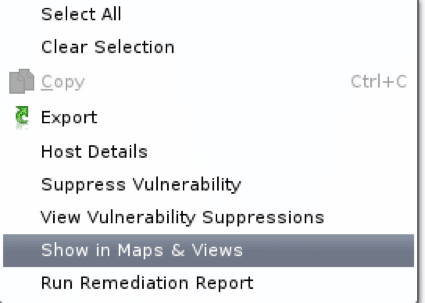
- In the bottom details pane, you will get a list of hosts that are affected by the MOVEit vulnerability. Right click on a device and select “Show in Maps and Views”:
- Now that you have identified which subnets these hosts live on, you can run detailed path queries from “Untrusted” to the subnet and IP in question, on TCP ports 80 and 443, to find out which firewalls are in the path and should have blocks placed on them.
Alternative Steps
An alternative method to obtain a comprehensive list of network segments is to use the Zones and Policies feature in RedSeal. Following steps 1-4 above:
- Set up a new view in Zones and Policies and have Group A be “Untrusted”, and Group B be “Affected Hosts”.
- Add all your Untrusted Subnets to the “Untrusted” group, and all the hosts to your “Affected Hosts” group.
- Set up access rules between the two, such as “Approval Required”, or “Access Forbidden”, and run analysis.
Once complete, you will have a comprehensive listing of every source that can get to the specific destinations, and even run detailed path queries directly from that menu to find your firewall rules.