From Reactive to Proactive: Transforming Healthcare Cybersecurity Post-Change Healthcare Attack
Change Healthcare, a major player in the healthcare technology sector, fell victim to a ransomware attack in February and is quickly heading towards a billion dollars in loss. The breach disrupted its operations and potentially compromised sensitive patient data. The attackers, ALPHV, also known as BlackCat and Noberus, exploited vulnerabilities in the company’s IT infrastructure, likely through phishing emails or other means, to gain unauthorized access to their systems. This breach not only posed a significant threat to patient privacy but also raised concerns about the integrity of healthcare data and the reliability of essential services.
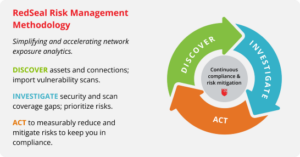
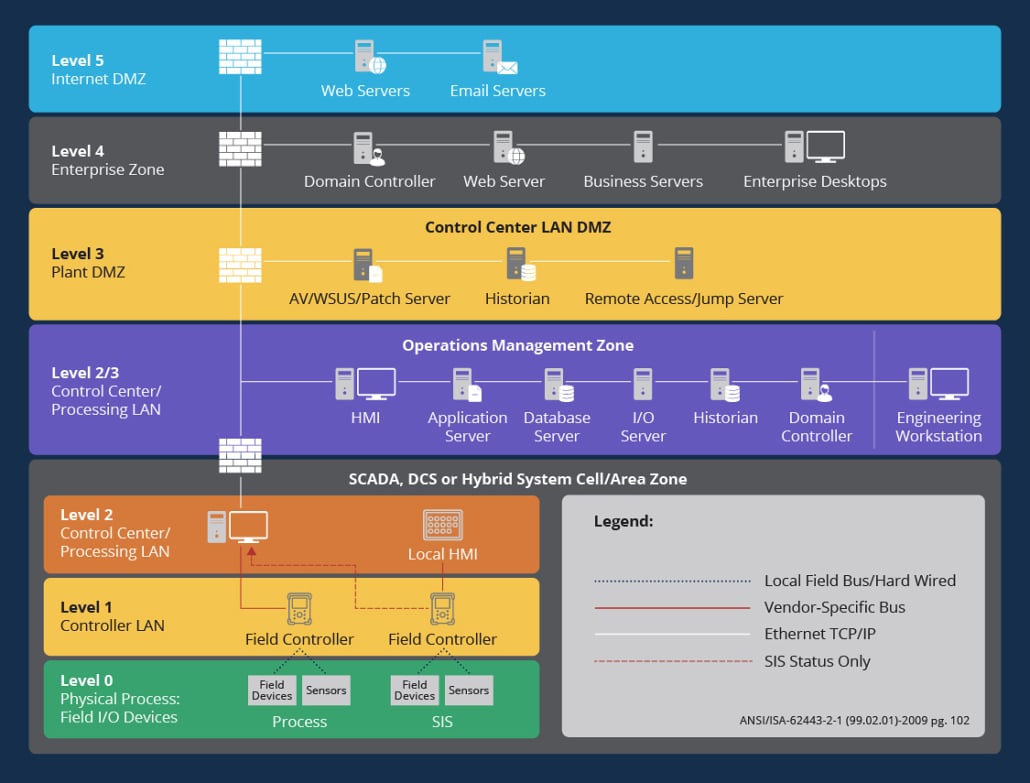
In the landscape of healthcare, where interconnected IT, operational technology (OT), and Internet of Things (IoT) networks are the norm, it’s inhumanly difficult to understand the whole attack surface. This is why experts and regulators advise adopting a proactive approach to security with best practices including segmentation – keep separate things apart, so that an attacker cannot easily spread from one place to another. Defenders of healthcare networks need automated assessment of their defensive posture, to uncover gaps and ensure good hygiene ahead of the next attack.
Healthcare administrators must fortify network infrastructure with stringent policies, including robust password enforcement, firewall configurations, and access controls. Vigilant monitoring and configuration of all connected devices, from medical equipment to personal devices, are imperative. Employing strong encryption further enhances data security, deterring cyber intrusions.
Another best practice is implementing a framework such as NIST and MITRE ATT&CK as part of your comprehensive cyberdefense efforts. Take for example another high-growth healthcare organization. Managing 20,000 clinicians and 150,000 medical devices, taking a proactive approach to network visibility and vulnerability prioritization is critical. As cyberattacks have become more sophisticated, healthcare organizations must be proactive and adopt best practices to, as this health system’s cybersecurity expert put it, “prepare the battle space.” In addition to having a dynamic map of their environment, the health system relies on the MITRE ATT&CK (adversarial tactics, techniques, and common knowledge) framework, a comprehensive knowledge base that gives security personnel key insights into attacker behavior and techniques, to help it prevent potential attacks and keep patient information, payment information, and other key data secure.
Click here to read the full case study
Regular attack surface scans are essential for proactive risk mitigation, providing crucial insights for informed decision-making in cybersecurity strategy development. Prioritizing rigorous testing of all software and device updates is crucial to preempt vulnerabilities.
Secure your healthcare network comprehensively with RedSeal. Our network exposure analytics platform offers dynamic visualization of network ecosystems, empowering organizations to identify and address vulnerabilities efficiently. Partnering with leading infrastructure suppliers, we deliver unparalleled network security solutions and professional services, ensuring robust protection against evolving threats.