Protecting PHI, Challenges and Solutions for Healthcare
What is data worth? On the surface, it is just a bunch of 1s and 0s on a hard drive. Most users don’t think about or even fully understand data. Their cell phones work, email is at their fingertips, and a friend is just a video chat away. But, enormous companies are built using data. Data is a big driver of economy, advertising, and business decisions. On the darker side, data is a target for attackers, who find a large market for it.
When it comes to personal data, is your credit card or your health information worth more? According to the Ponemon Institute[i], health records have sold for $363 per record — more than the price of stolen credit cards and service account credentials combined! 2015 was known for healthcare mega-breaches. It’s estimated that half of US citizens’ medical information is available for purchase, with 112 million records becoming available in 2015. Supply and demand works here, too. Due to the large number of records available on the black market, the price has dropped significantly in recent months. This doesn’t mean the healthcare industry is out of the woods. According to McAfee Labs[ii], healthcare attacks are increasing even though the average price per record is dropping.
Personal health information (PHI) is attractive because it lasts longer and is more difficult for victims to protect. Unlike the credit card industry, the healthcare industry hasn’t come up with a good way to stop and prosecute fraudulent charges. If you see your credit card is used by someone else, you can call up and have the charges reversed and a new card issued. This isn’t the case with your PHI. Likewise, it is more difficult to see if your PHI was used to buy drugs or equipment. How often do you check your medical bills compared to your credit card statements? Additionally, PHI opens the door for attackers to steal victims’ identity, or buy and sell medical equipment and drugs with the stolen information. Because they have such valuable information, healthcare organizations must take an active role in protecting their data, yet not close it down so tightly they can’t remain in business.
Recently, I went on Shodan, a search engine that scours the internet and gathers information about all connected devices. It isn’t secret; anyone can use it to search for vulnerable devices. In the US alone, I found hundreds of devices belonging to organizations that handle sought-after health information. These organizations used insecure protocols, services, and software with known exploits — illustrating the seriousness of this problem.
The healthcare industry must overcome the same challenges other industries face. It is only unique in the value of its data. Lack of finances, expertise, and time all compound the problem. I call this the Security Triangle (a spinoff of the Project Triangle). You have expertise, time, and finances and you only get two. RedSeal can help healthcare organizations balance out this security triangle. When a healthcare organization installs RedSeal, the automation it provides will free up their experts to handle other pressing issues.
RedSeal will parse through the configurations of multiple vendors and visualize all paths from the internet to the inside of your network. RedSeal offers a single pane of glass for your network, vulnerabilities, best practice checks, and policies, to simplify the understanding of information flows. You can set up RedSeal to alert you if your organization is at risk from an insecure protocol being accessible to the web. Without RedSeal, this process is painstakingly manual, requiring a great deal of time and resources to fully understand.
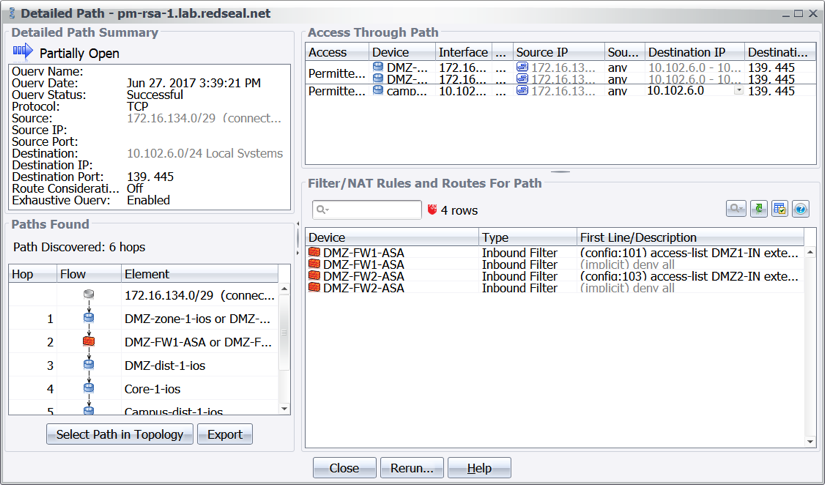
With RedSeal in your network, you can ensure that your organization’s policies are followed. If there are any changes that increase the risk to the organization, the dashboard will alert you. Organizations that keep medical data can set up policies to alert them if internet devices can directly access medical records, or if they can leapfrog into the network through some other server. Normally this requires a plethora of tools or manual labor, making the process complex. Once configured, RedSeal will automatically check policies to ensure access to critical systems remain as configured. If new access is introduced, the dashboard will alert you — saving time and resources, and freeing up your experts to more urgent tasks.
Healthcare organizations using RedSeal can automate manual tasks and improve security, freeing up their resources to take on more urgent matters — saving lives.
[i] https://www.csoonline.com/article/2926727/data-protection/ponemon-data-breach-costs-now-average-154-per-record.html







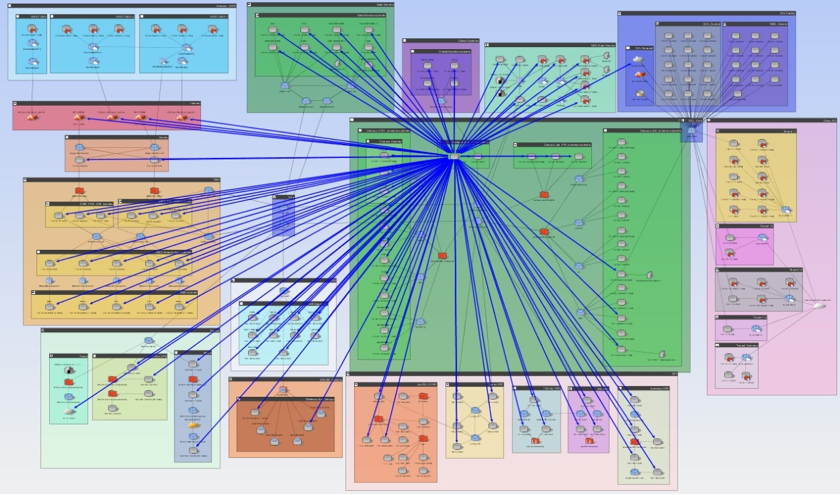 Figure 1: Visualizing all accessible areas of the network from a compromised system.
Figure 1: Visualizing all accessible areas of the network from a compromised system.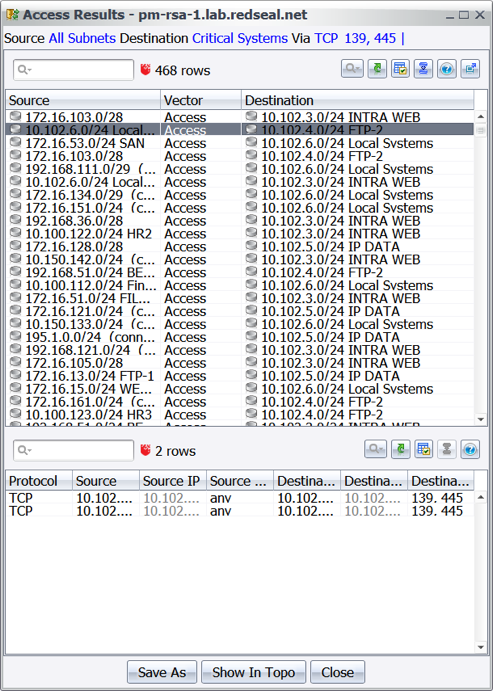 Figure 2 Results of an access query revealing what access exists from all subnets leading to the critical assets over TCP 139 or 445.
Figure 2 Results of an access query revealing what access exists from all subnets leading to the critical assets over TCP 139 or 445.