Credit unions continue to be the primary targets of cyberattacks like phishing, ransomware, and supply chain attacks. This is due to the highly confidential nature of the data they collect and store. If this data falls into the wrong hands, the outcome can negatively impact the institution’s reputation, as well as its legal and financial standing.
Cyberattacks aimed at credit unions come at a high cost. Financial loss can range from $190,000 for small credit unions to as high as $1.2 million for large credit unions.
As technology advances, so have the cyber threats targeting credit unions. The National Credit Union Administration (NCUA) has continuously encouraged credit unions to “strengthen their institution’s cyber vigilance and preparedness efforts” to protect themselves and their members.
Read on to learn how credit unions can mitigate cybersecurity risks. The key is to first understand the primary threats and then how to reduce their impact.
Cybersecurity Trends in the Finance Sector
Over the last decade, cybercriminals have found creative ways to target credit unions. Attacks have increased in volume and severity, with hacking and malware being deployed to cripple financial institutions. The first half of 2020 saw a 238 percent increase in cyberattacks targeting the finance sector.
Between March and June of 2020, ransomware attacks aimed at banks increased by 520 percent compared to the same period in 2019. A huge spike was also observed in 2021.
In June of this year, several credit unions in Canada discovered evidence of attempted access by unauthorized personnel. A 2020 survey by the National Credit Union Administration (NCUA) found that 46% of credit unions experienced a cybersecurity incident in the past year. Phishing attacks continue to be a major threat to credit unions, with the NCUA reporting that they accounted for over 50 percent of incidents in 2020.
According to a recent IBM report, the average cost of a data breach in 2022 was $4.35 million. The finance sector is a primary attack target, only second to healthcare organizations, with the average financial breach costing $5.97 million. Credit unions, as a result, are increasingly turning to technology to improve their cybersecurity posture.
Credit unions should also be aware of the risk employees or contractors with access to sensitive information pose to cybersecurity. They can potentially misconfigure servers, networks, and databases and become compromised by hackers. Combating this may involve implementing measures such as keeping an updated inventory of cloud resources, reviewing misconfiguration by identifying unintentionally exposed resources, and reviewing security policies.
With large amounts of money at risk, following cybersecurity best practices can help credit unions stay on top of cyber threats.
Common Cyber Challenges for Credit Unions
Credit unions and financial institutions face a wide range of cybersecurity dangers and challenges — from hackers looking to exploit loopholes to sophisticated cyber warfare/cyber espionage maneuvers of advanced persistent threat (APT) actors.
Learning about the potential risk factors can help credit unions mitigate these risks.
Here are the most common cybersecurity challenges credit unions should be aware of.
Sophisticated Cyberattacks and Ransomware
A ransomware attack, which involves encrypting files and locking users out of their systems, happens every 11 seconds. Criminals then demand a ransom to release the data. Credit unions must have strategies in place to ensure their systems are protected from such attacks.
Ransomware attacks not only cause credit unions to lose large amounts of money in ransom payments and fines; they also erode consumer trust. In most cases, ransomware attacks happen because employees fall for phishing scams that trick them into downloading suspicious attachments, clicking malicious links, or launching sketchy .exe files.
By regularly assessing and analyzing your entire system, you’re better able to spot any new vulnerabilities and emerging threats. It’s also important to educate employees and customers about cybersecurity best practices so they are equipped to handle various types of cyberattacks.
Supply Chain Interruptions via Third-Party Vendors
Credit unions typically use third-party partners to offer better features and functionalities to their members. Cybercriminals take advantage by attacking less secure software vendors. These vendors then inadvertently deliver malicious code in the form of compromised products or updates, enabling cybercriminals to access the credit institution’s network.
To minimize this risk, credit unions should thoroughly vet vendors before entering into a business partnership with them. They should also scrutinize their security practices and perform regular system updates and maintenance to ensure their existing infrastructure performs optimally for the longest time possible.
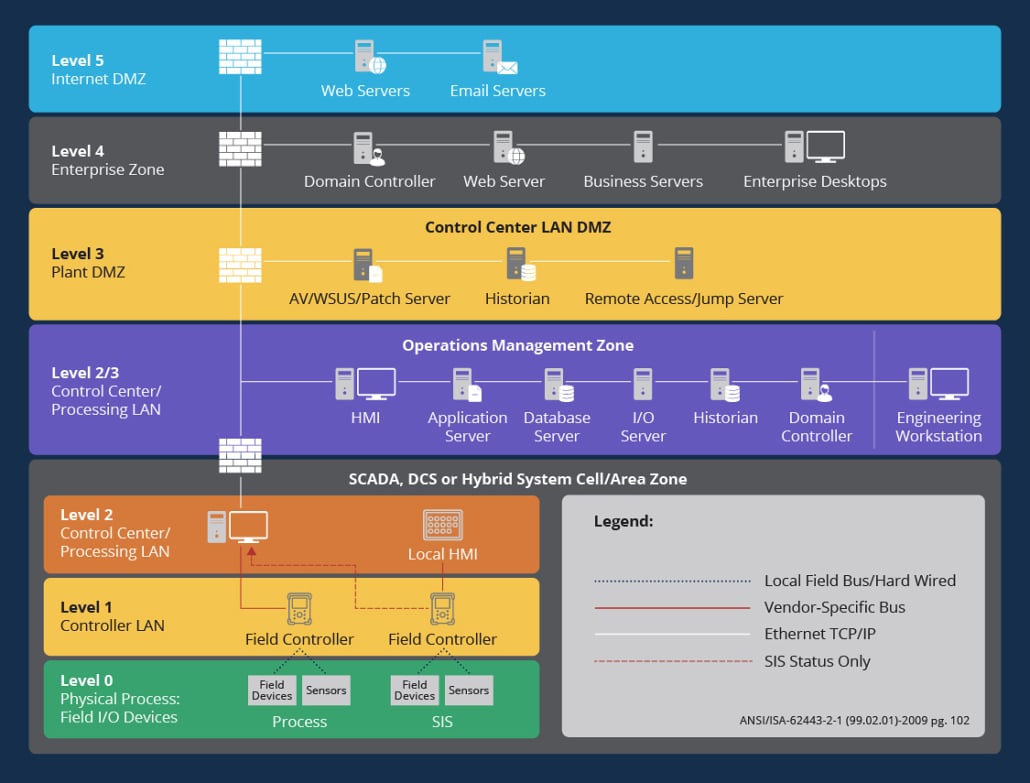
Emerging Threats Associated with the Internet of Things (IoT)
Hacking techniques are continuously becoming more sophisticated. IoT adoption is increasing exponentially, and hardware assets connected to the internet such as cameras, printers, sensors, and scanners are becoming a major target of exploitation by cybercriminals.
With over 50 percent of all IoT devices susceptible to severe cyberattacks, credit unions should focus on investing in cybersecurity solutions that make it easier to identify all IoT devices connected to their network. This way, they can easily monitor IoT devices for any security issues and take action before the risks become harder to mitigate.
Shortage of Cybersecurity Skills
The demand for cybersecurity experts, especially among credit unions, is outpacing the supply of qualified professionals. According to the 2022 (ISC)2 Cybersecurity Workforce Study, even with an estimated 4.7 million professionals, there’s still a global shortage of 3.4 million workers in this field. This will affect smaller credit unions as they will find it difficult to hire expertise well-versed in various cloud technologies.
Technical skills such as secure software development, intrusion detection, and attack migration are by far the most valuable skills in this field. Security teams in the credit union space must look for innovative solutions to optimize productivity. This includes identifying security tools and technologies that are easy to use and deploy, providing more opportunities for external training, and identifying solutions that streamline cybersecurity processes.
How Credit Unions Can Strengthen Their Cybersecurity
To ensure your credit union has optimal protection against potential cyberattacks, RedSeal recommends a proactive approach by performing regular cybersecurity assessments to identify any loopholes in your system and also ensure proper defenses are in place. These include having an up-to-date inventory, identifying unintended exposures, and setting a security baseline to meet current and future compliance requirements. It’s also important to establish security protocols that follow industry guidelines and continuously apply security patches and updates to the system.
Working with a prioritized set of risks allows security teams to better allocate resources to areas where they’re needed most.
Want to know more about how you can mitigate cyberattacks in your credit union? Check out this white paper on digital resilience and ransomware protection strategies.